I’ve been working with some colleagues at Northeastern University (NEU) in Boston, MA, on ways to combine CSP with machine learning. The work I’m doing with Old Dominion University is focused on basic modulation recognition using neural networks and, in particular, the generalization (dataset-shift) problem that is pervasive in deep learning with convolution neural networks. In contrast, the NEU work is focused on specific signal detection and classification problems and looks at how to use multiple disparate data types as inputs to neural-networks; inputs such as complex-valued samples (IQ data) as well as carefully selected components of spectral correlation and spectral coherence surfaces.
My NEU colleagues and I will be publishing a rather lengthy conference paper on a new multi-input-data neural-network approach called ICARUS at InfoCom 2023 this May (My Papers [53]). You can get a copy of the pre-publication version here or on arxiv.org.
The problem is to detect the presence of a low-level direct-sequence spread-spectrum signal that is cochannel with a conventional wideband signal such as LTE. Because the spread-spectrum signal is designed to be demodulatable even when the inband noise and interference power is tens or hundreds of times that of the signal, it can hide, effectively, underneath the innocuous conventional communication signal, and still be received and demodulated by its intended receiver with adequate bit-error performance.
The ultimate goal is the construction of a fusion pipeline, which is machine-learning terminology for a neural network that can take in disparate data types, such as IQ data and a cycle-frequency list. But it is also of interest to compare the performance of such a construction with marginal, or single-input-type, networks (pipelines). Therefore, four distinct pipelines (algorithms) are defined:
- Signal-processing only. Here we use only CSP products and simple signal-processing algorithms to detect the presence of the anomaly.
- Trained neural network using only IQ samples as input.
- Trained neural network using only CSP products as input.
- The fusion pipeline: a trained neural network that makes use of both IQ samples and CSP products.
The detection performance is summarized in the paper’s Table II, which is reproduced here as Figure 1.

A couple things to note, briefly, because I want you to go look at the full paper.
CSP doesn’t work so well compared to the pipeline that uses only IQ data (where have we seen that before?). This is similar to other published results that don’t take into account the highly brittle nature of networks trained on IQ data–they don’t generalize. But we didn’t try to include generalization here in My Papers [53]; we’ll get to that eventually though. (In other words, we don’t report “trained on Synthetic, tested on OTA-Cellular,” or the like.)
The second thing is that performance generally is quite dependent on the particular kind of LTE signal involved in the training and performance evaluation. We have three basic types of LTE data: synthetic (MATLAB), PAWR (captured), and wild/cellular (captured). The synthetic data is from the MATLAB LTE toolbox, the PAWR data is from an NEU testbed that uses srsLTE, and the cellular data is captured using an Ettus SDR pointed at various cellular bands in Monterey, CA. The spectral signature of the srsLTE signals is different from the other two, and it produces a huge number of cycle frequencies, overwhelming the signal processor’s ability to sort out the DSSS cycle frequencies from the LTE cycle frequencies. But this is quite helpful information because it goes, yet again, to generalization. You can’t just say “LTE” and mean much by it. Even though each of the three types of LTE signals might be demodulatable by the very same LTE receiver, they are still different in other important ways.
Finally, it is satisfying, and a testament to the ingenuity of my co-authors, that the fusion network always performs best.
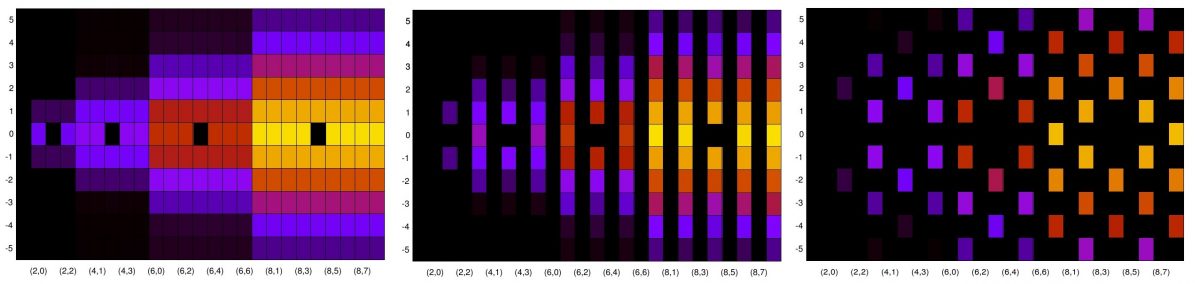
Pipelines 2-4 also can perform modulation recognition in terms of specifying whether the detected DSSS signal is DSSS BPSK or DSSS QPSK. The high-level results are summarized in the paper’s Figure 7, which is reproduced here as Figure 2.

There are several strange trends in the bar graphs of Figure 2, and I don’t have good explanations of them. I believe that this means we still have a lot of work to do to really solve the stated problem. But the paper represents a solid step forward.
A good chunk of the paper is devoted to the problem of choosing one of these pipelines under various constraints on inference time and computational cost. This kind of guidance will be increasingly important as, over time, we improve the performance of all the pipelines, and perhaps introduce new ones with different performance/cost/latency tradeoffs.
Go take a look, and maybe I’ll see you at InfoCom!